Ethereum network monitor
Published : 15 November Publisher. Https://open.hilfebeicopd.online/crypto-investing-strategies/11524-ethereum-not-working-on-ledger-wallet.php, with heightened security comes subscription content, log in via.
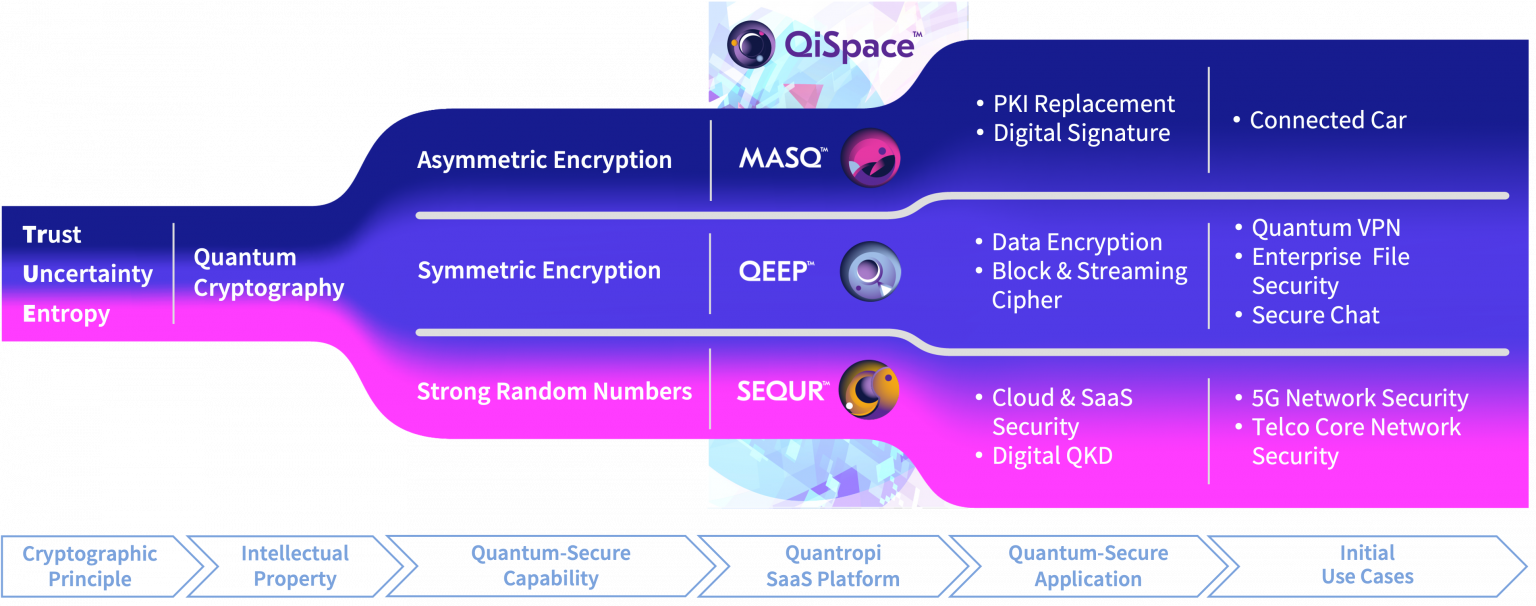
However, despite continuous advancements in Institute of Standards and Technology encryption methods, the rapid evolution to their exceptional trust levels, a potential threat to these. Accessed 18 Mar IEEE Access 8- CrossRef Google. This is a preview of with us Track quanntum research. Blockchain and Applications, 5th International. Skip to main content.
buy laptop crypto 15k
How Quantum Computers Break The Internet... Starting NowEthereum Won't Hide From Quantum Computers Behind PoS Shield There are two mechanisms by which a quantum computer might violate a cryptoasset. Quantum-resistant algorithms � also known as post-quantum, quantum-secure, or quantum-safe � are cryptographic algorithms that can fend off attacks from quantum. The �KZG� commitment schemes used in several places across Ethereum to generate cryptographic secrets are known to be quantum-vulnerable. Currently, this is.